Cybersecurity in Pterodactyl: Protecting Your Game Servers
Learn best practices for securing your Pterodactyl panel and game servers. Implement strong authentication, SSL/TLS, and access controls.
Introduction
Pterodactyl is a powerful open-source game server management panel that allows administrators to manage multiple servers efficiently. However, with great power comes great responsibility—security should be your top priority.
This comprehensive guide covers essential security measures to protect your Pterodactyl infrastructure from common threats and best practices for maintaining a secure environment.
Why Pterodactyl Security Matters
Game servers often handle sensitive player data and require reliable uptime. A compromised Pterodactyl panel can lead to:
- Data breaches exposing player information
- Unauthorized server access and modifications
- Service disruptions affecting player experience
- Financial losses from resource abuse
- Compliance violations with data protection regulations
SSL/TLS Encryption
Always use HTTPS for your Pterodactyl panel:
# Using Let's Encrypt with Certbot
certbot certonly --standalone -d panel.example.com- Enable HSTS headers
- Use modern TLS versions (1.2+)
- Keep certificates updated
Authentication & Access Control
Strong Passwords & 2FA
{
"password_policy": {
"minimum_length": 12,
"require_uppercase": true,
"require_numbers": true,
"require_special": true
},
"2fa_enabled": true,
"session_timeout": 1800
}API Key Management
- Generate unique API keys for integrations
- Rotate keys periodically
- Limit key permissions to necessary scopes
- Monitor API key usage
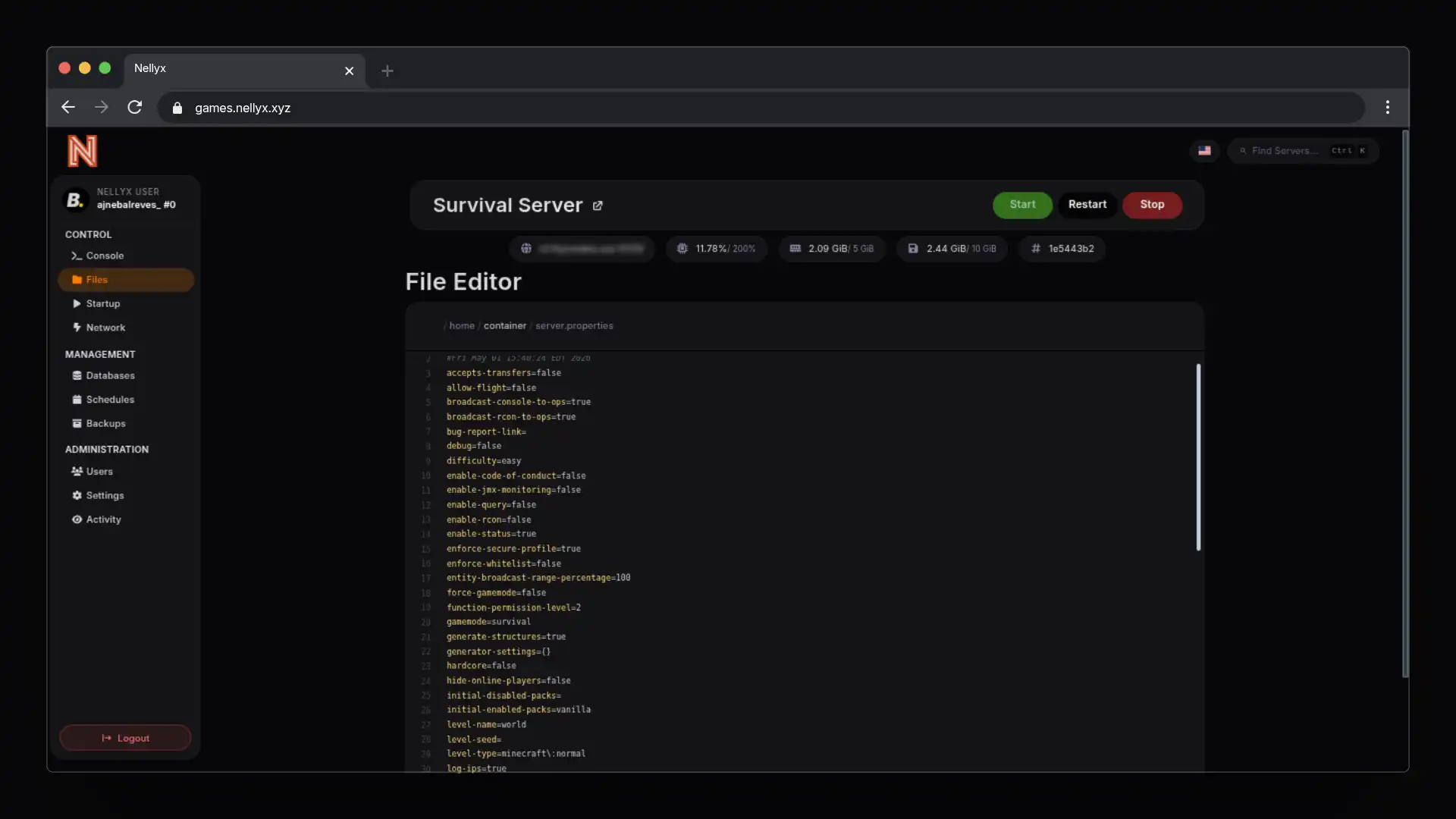
Firewall & Network Security
Restrict access to your Pterodactyl infrastructure:
- Use UFW or firewalld for host firewall
- Implement reverse proxy (nginx/Apache)
- Set up fail2ban for brute-force protection
- Use private networks where possible
Regular Updates & Maintenance
# Keep Pterodactyl updated
cd /var/www/pterodactyl
php artisan down
curl -L https://releases.pterodactyl.io/installer.sh | bash
php artisan upDatabase Security
- Use strong database passwords
- Enable database encryption
- Regular backups with encryption
- Restrict database access to local connection
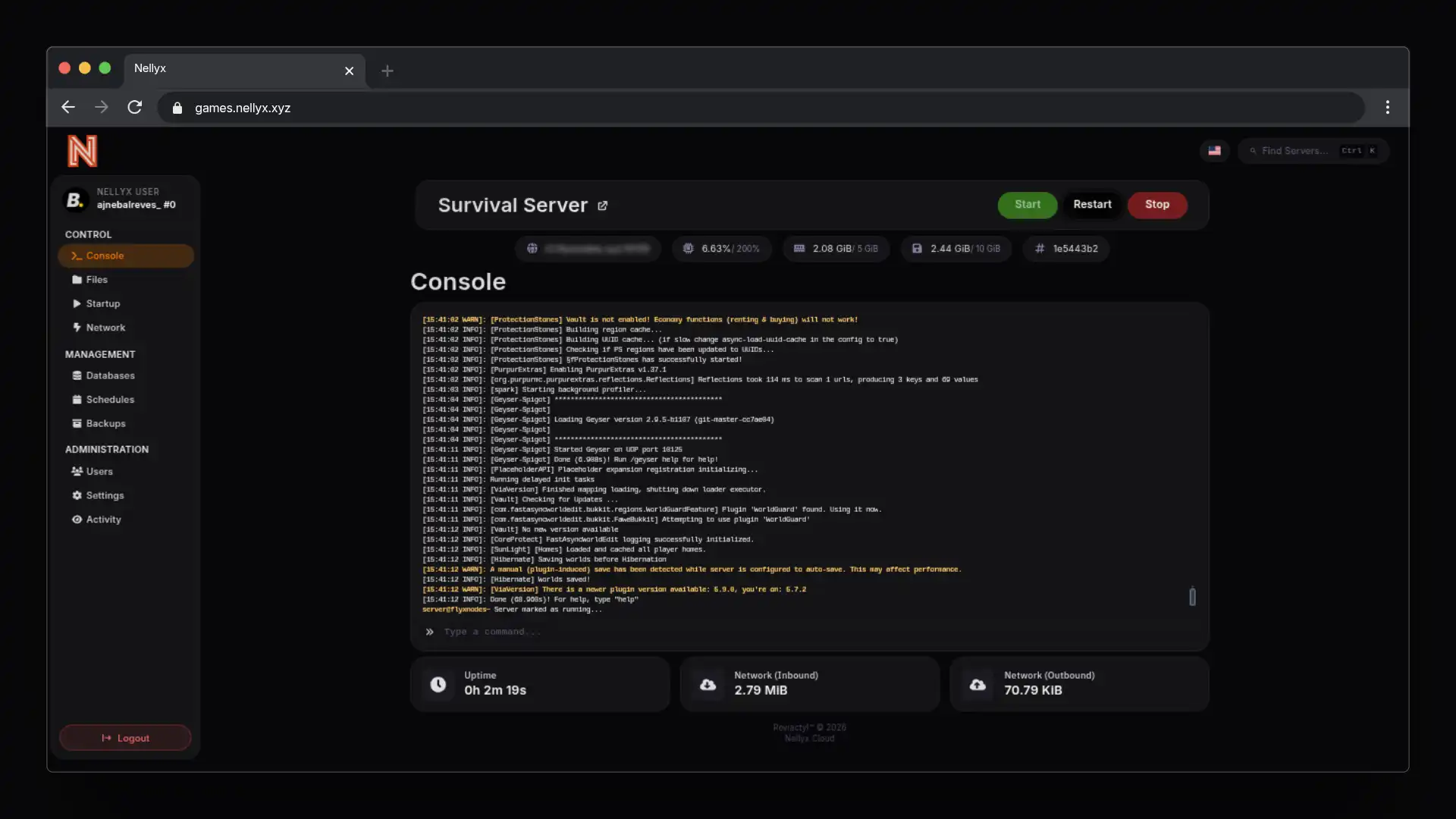
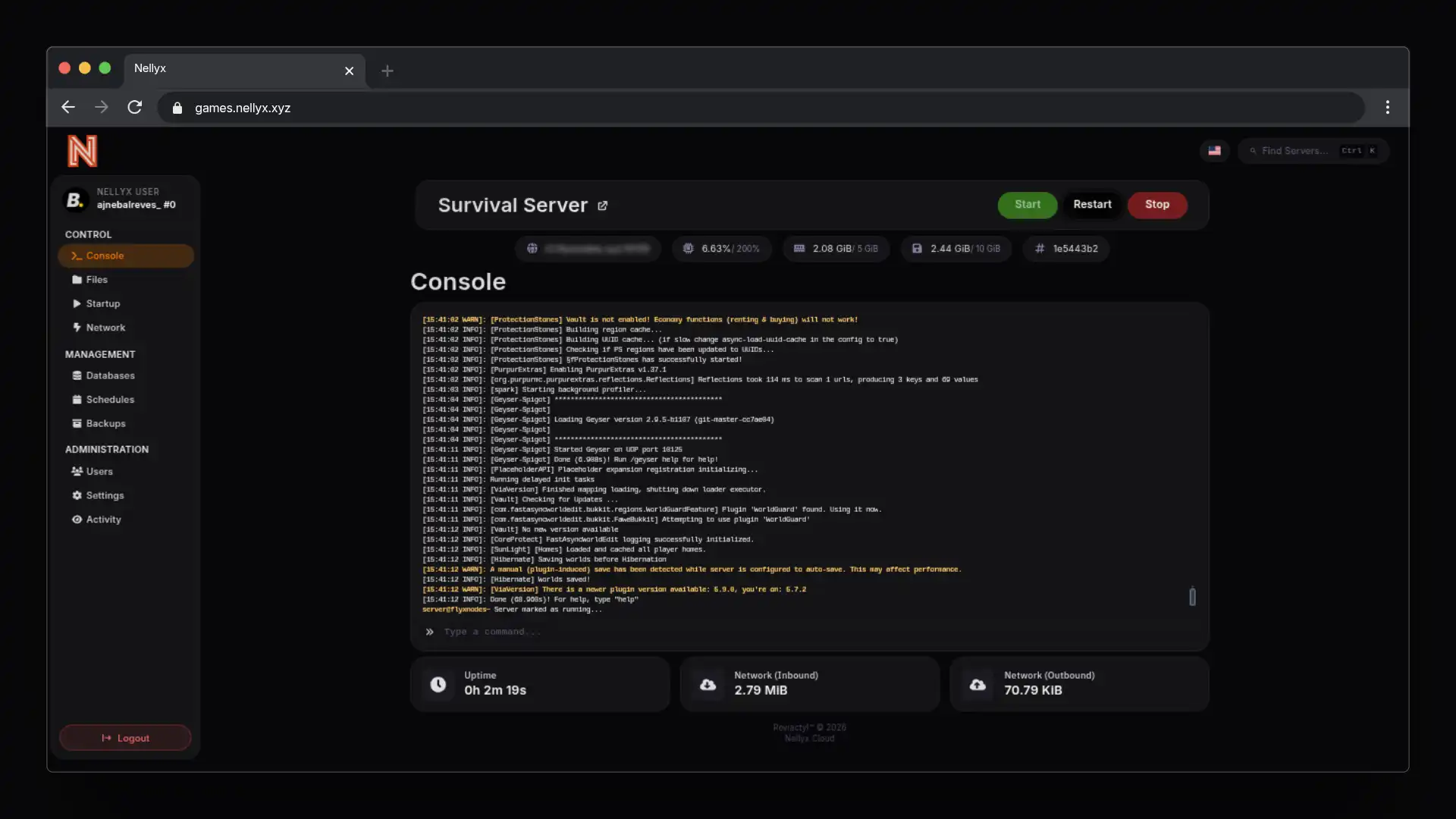
Monitoring & Logging
Implement comprehensive logging to detect suspicious activity:
- Application logs
- System audit logs
- Failed login attempts
- API access logs
- Database queries
Conclusion
Securing your Pterodactyl panel is an ongoing process. Follow these best practices, stay updated with security patches, and regularly audit your infrastructure for vulnerabilities.
Remember: Security is not a feature, it’s a process.
Related Articles
Understanding DDoS Protection: How Nellyx Keeps Your Servers Safe
Learn how DDoS attacks work and how Nellyx helps protect game servers from common attacks.
Game Server Performance Optimization: The Ultimate Guide
Maximize your game server performance with these proven optimization techniques. From tick rates to network configuration.